
Back in April of this year, NBC news reported of a family that had an internet enabled baby monitor that was hacked by an intruder. The two parents of the home awoke to the sound of a man screaming at their 10 month old little girl from within her room. The man was screaming, “Wake up baby!” in addition to a number of expletives. If you want to talk about psychologically scarring a child, I can foresee 10 years down the road, this little girl being petrified of anything connected to the internet.
These kinds of risks are not specific to baby monitor cameras. Essentially, anything that is connected to the internet comes with a level of risk of being accessed from the outside world. While there is no way to make your network 100% secure, there are a number of best practices that can keep your network more secure.
Now, before you go crazy investing in internet security, the other thing to keep in mind is motive. The effort required to secure your network should match the amount of risk you face. This can be measured by assessing the amount of motive there is out there to be hacked by someone. For example, the risk of Angelina Jolie’s webcam being hacked is far greater than your average citizen due to the monetary value of those images to reporters and fans alike. I’m going to recommend a few different techniques that you can use without having to invest heavily to secure your home.
Additionally, this article is a bit lengthy and includes a number of different techniques for securing your home network. Don’t be overwhelmed, take your personal internet security initiative one step at a time.
Disable Connection From The Internet (When Applicable)
In the example of the family featured on NBC news, theintruder likely used a program that scans IP addresses for open ports that have security and web cameras connected to them. Now, I own a similar camera by the same brand that I use for my own baby monitor. To be able to connect to the camera over the internet, you have to configure your router in a specific way to allow direct access over the internet. Enabling that enables anyone with an IP address sniffer to connect to your camera.
The easiest way to limit this risk is not to allow a connection over the internet. Consider the use case, when are you going to need to leave your child in the crib and go somewhere outside of your network? The correct answer to that question should be “never.” What good does a baby monitor do if you can’t attend to your baby when in need. The rule of thumb here is, even if your device supports a feature, that doesn’t mean you should always use it; especially if it opens up vulnerability.
Change the Default Username and Password
Now, you may not be using your camera or device to monitor a baby, for example security cameras. You may want to be able to access that camera over the internet. It is likely that our NBC family was using the default username and password that came with the camera. This makes it really easy for anyone that sniffs out your camera to gain access to it. This rule doesn’t only apply to your devices, but also to your router/modem itself.
The default login and password to the administrative section of a router is typically “Admin” and “password” respectively. What this does is allows anyone that connects to your network, the ability to open a back door to your connection. By opening a specific port or even enabling what’s known as a DMZ to a device on your network, this opens that device to a world of vulnerability. Best rule of thumb, change the default login to your password, and the default Wi-fi password to your router.
Encrypt Your Wireless Network
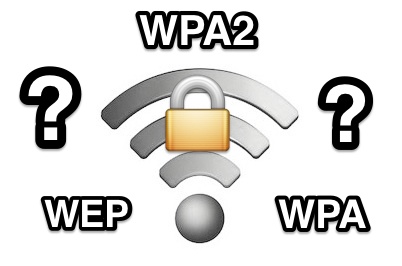
Encrypt is a fancy word. For a wireless network, it basically means putting a password with a level of security over the connection to keep unwanted people out of your network. There are a number of different types of encryption each with their own specific algorithm, or way of keeping people out. When you’re configuring your Wi-Fi password, you are likely to see three different options: WEP, WPA, and WPA2.
WEP: WEP is the oldest algorithm that has been shown to have flaws in the way it protects. It was so flawed that back in 2001, the FBI gave a public demonstration of them using free software to crack the password of a WEP encrypted connection in under a minute. While it has evolved and improved over time, it is still the most vulnerable type of encryption on the market. It’s also worth noting that the Wi-Fi alliance retired WEP encryption back in 2004. If your modem only supports WEP, it’s time to go buy a new modem.
WPA: WPA encryption was released as an answer to WEP’s problems. It had a number of new algorithms that increased the amount of security. It was designed, however, to be released as a firmware update to existing WEP modems. Due to that, the backbone of this type of encryption relied upon the WEP encryption programming which enabled exploited over time.
WPA2: WPA2 was the predecessor to WPA that addressed many of the issues of WPA, however, there are still a number of holes that remain from the original WPA encryption. According to Howtogeek, using the exploits in this algorithm can take anywhere from “2-14 hours of sustained effort with a modern computer” to gain access to your network.
Now, I’m sure your thinking, 2-14 hours of sustained effort can allow someone into my network even with the best encryption on the market? The answer is, “yes.”
WPS: That is why a function called Wi-fi Protected Setup, or WPS, was invented. Essentially, this function requires that you physically press a button on your modem prior to connecting any new devices. What this means is that if an intruder wants to breach your network, they are going to have to breach your property first. You may even want to put your modem into a padlocked closet somewhere for added security from suspicious guests. Check with your wi-fi router/modem manufacturer to find out if your modem supports WPS as well as how to enable and use it.
Upgrade the Firmware/Software

Another way in which intruders often get access to your computer/devices is through security holes in software that you have installed on your computer. For this reason it is critical that you keep your software up-to-date. For example, that annoying pop up that says you have a Window’s Update to install. While clicking delay so that you can pin the next big thing on Pinterest may be tempting, you may be risking your identity being stolen by someone gaining unauthorized access to your computer. The best rule of thumb, install those updates as soon as they release. Security holes are one of the most common reasons for a Window’s Update release.
This same rule applies to other devices such as smart phones and even wi-fi devices such as your baby monitor. In the example of our NBC family, they had a 3-year-old camera with outdated firmware that enabled the intruder access.
Filter By Mac Address
Another excellent feature of many routers is to create a list of acceptable devices that can connect to the network. Every internet connected device has its own unique Media Access Control (MAC) address. This is unchangeable and is hard-coded to each device. This is another excellent way to protect against intruders, though it is not spoof-proof. Intruders with enough motive can gain access to your router, see the available MAC addresses and make their computer appear to have an acceptable MAC address. This takes a lot of effort, and again, the motive needs to be there.
This method can be a bit annoying as any guest that wants access to your network will require a log in to the router and adding their specific MAC address to the white-list of accepted devices. If you’re using WPS, I don’t personally think you need to filter by MAC address as it is easier to just push a button on your router to allow a connection rather than logging in and entering a lengthy code. That’s just my opinion though.
Hide Your SSID

Another way to protect yourself is to hide the SSID of your modem/router. The SSID is the name that pops up whenever you search for wireless networks. If it is hidden, it won’t pop up during a search and you’ll have to enter and match the exact name of the network manually. Keep in mind that this does not make you invisible and again, someone with enough motive can discover your network. This will, however, likely keep your 11-year-old neighbor hacker hobbyist from access your network.
Conclusion
You may be overwhelmed with all of the different ways you can secure your network. I would start with assessing the amount of risk and then using a few of the best practices mentioned above. If you’re using WEP encryption, get that changed as soon as you can, then move on to some of the other methods.
What do you think about the above techniques? Are there any other methods that you have found to be effective? Let us know in the comments below.
